Wireshark
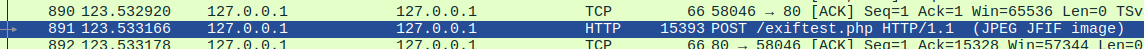
Look for web requests in .pcap files. These can be a treasure trove for enumeration.
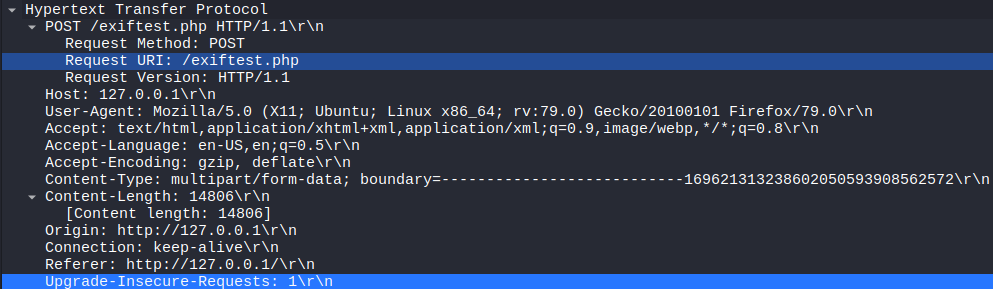
Looking at the HTTP section of the intercept shows us the same headers and content we'd see from curl or Burpsuite.
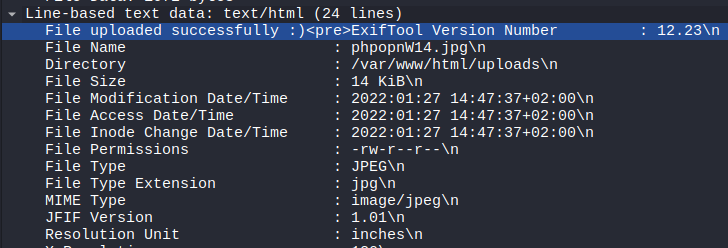
Also check Line-base text data. This will be the body of the request and will contain form fields too. Note the exposed vulnerable version number in this example.